Unlocking the Power of Nutanix Cloud Clusters (NC2): Sizing and Deployment on Azure and AWS10/18/2023 Navigating the dynamic landscape of cloud computing requires solutions that offer flexibility, simplicity, and cost-efficiency. Nutanix Cloud Clusters (NC2) emerges as a beacon of innovation in the hybrid multi-cloud realm, providing a comprehensive platform that caters to diverse cloud deployment needs. This extensive guide dives deep into the world of NC2, exploring its intricate details, highlighting its advantages, and illuminating its deployment intricacies on Azure and AWS. Whether you are planning a migration to the cloud or optimizing your current cloud infrastructure, NC2 is a force to reckon with. Demystifying Nutanix NC2Nutanix Cloud Clusters (NC2) stands as a testament to the evolution of cloud technology, bringing together the prowess of Nutanix's hyper-converged infrastructure (HCI) stack – comprising Nutanix AOS, AHV, and Prism – into the public cloud arena. It accomplishes this feat by running on bare metal instances, facilitating seamless application migration from on-premises environments to renowned public cloud providers like Azure and AWS. The Multifaceted Benefits of NC2
Exploring NC2's Use CasesThe versatility of NC2 makes it an invaluable asset for organizations. Here are some practical use cases:
Comparative Analysis: NC2 vs. VMware OfferingWhile Nutanix Cloud Clusters (NC2), VMware on AWS, and VMware Cloud on Azure all offer hybrid cloud solutions for running VMware workloads, each presents distinct characteristics:
Nutanix Cloud Clusters (NC2):
0 Comments
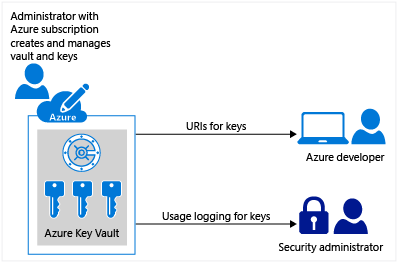
My customers are progressively embracing hybrid and multi-cloud environments to harness the advantages of a range of cloud platforms, including Microsoft Azure, AWS, and Google Cloud. While these configurations deliver unparalleled flexibility and scalability, they also bring about intricate cybersecurity hurdles. Within this blog, I will delve into the most effective strategies for fortifying hybrid and multi-cloud setups, with a particular emphasis on Microsoft Azure, to protect sensitive data and uphold a resilient cybersecurity stance. Best Practices for Securing Hybrid/Multi-Cloud Environments with Microsoft Azure:1. Implement Strong Identity and Access Management (IAM): To ensure authorized access and prevent data breaches, utilize Azure Active Directory (Azure AD) for centralized identity management. Enforce multi-factor authentication (MFA) and role-based access control (RBAC) to maintain fine-grained permissions. Regularly review and update user access privileges to mitigate the risk of unauthorized access. 2. Encrypt Data in Transit and at Rest: Protecting data is paramount. Utilize SSL/TLS for data transmission between services and implement Azure Key Vault for secure key management. Employ Azure Disk Encryption to safeguard data at rest within virtual machines and Azure Storage, providing an additional layer of protection. Azure Key VaultAzure Key Vault is a cloud service that provides a secure store for secrets. You can securely store keys, passwords, certificates, and other secrets. Azure key vaults may be created and managed through the Azure portal. Azure Key Vault offers the following features:
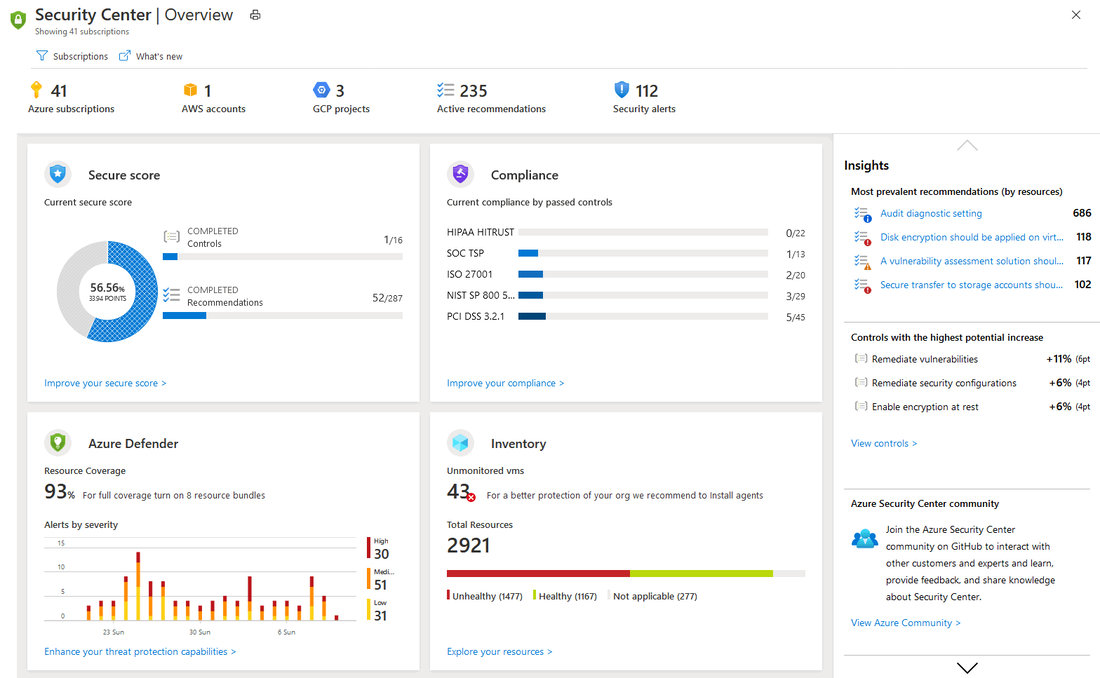
3. Network Security and Segmentation: Establish a secure network environment using Network Security Groups (NSGs) and Azure Firewall to control traffic flow between virtual networks and subnets. Leverage Virtual Private Networks (VPNs) or ExpressRoute for encrypted and private connections between on-premises and Azure resources, mitigating the risk of data interception. 4. Continuous Monitoring and Threat Detection: Stay vigilant by enabling Azure Security Center to monitor and detect threats across your Azure resources. Leverage Azure Monitor, Azure Log Analytics, and Azure Network Watcher for real-time monitoring and rapid incident response, ensuring timely action against potential security breaches. Azure Security CenterAs the cloud computing landscape persistently advances, businesses are required to maintain flexibility to keep pace. A growing number of my clients are finding it necessary to administer and operate within multi-cloud environments. Within this context, Nutanix Cloud Clusters (NC2) on Microsoft Azure present an effective solution for hybrid cloud infrastructures, facilitating businesses to streamline operations and maximize resources. In this blog, I will delve into the fundamental features and advantages of Nutanix Cloud Clusters on Microsoft Azure and examine how it can transform your corporate IT strategy. Furthermore, I will compare this with the Azure VMware Solution (AVS) and discuss how to get started on your journey with Nutanix Cloud Clusters. What is Nutanix Cloud Clusters (NC2) on Microsoft Azure?Nutanix Cloud Clusters on Microsoft Azure, or NC2, is a solution co-developed that facilitates seamless integration and management of private, public, and distributed cloud environments. It offers a unified infrastructure that allows businesses to move workloads between on-premises Nutanix clusters and Azure as per their convenience and requirements, providing true hybridity and mobility. Key Features of Nutanix Cloud Clusters on Microsoft Azure
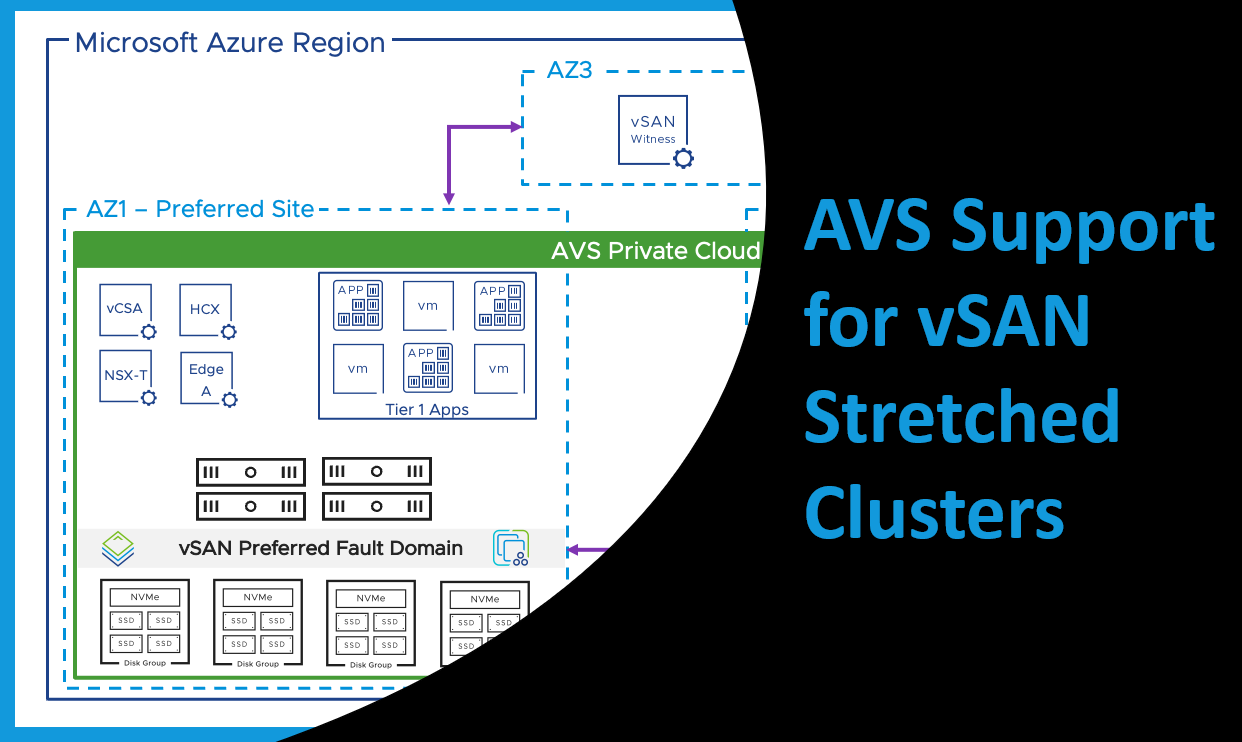
As businesses increasingly lean on technology, the need for continuous availability of critical applications and data has become vital. The interruption of IT operations can cause substantial financial and reputational losses to an organization. Therefore, implementing a robust business continuity plan that ensures uninterrupted operation of critical applications and data, even during a disaster, is imperative. One of the key technologies that support this requirement is VMware vSAN Stretched Clusters, which provide high availability and protection for mission-critical applications and data. Recently, AVS (Azure VMware Solution) support for vSAN stretched clusters has been made generally available in several Azure regions, including West Europe, UK South, Germany West Central, and Australia East. The Power of Stretched ClustersA stretched cluster is configured by deploying an AVS private cloud across two availability zones (AZs) within the same region, with a vSAN witness placed in a third AZ. This witness constantly monitors all hosts within the cluster, serving as a quorum in the event of a split-brain scenario. With an even deployment of hosts within the private cloud across regions, the whole system operates as a single entity. Leveraging storage policy-based synchronous replication, data is replicated across AZs delivering a Recovery Point Objective (RPO) of zero. Thus, even if one AZ faces disruption due to an unforeseen event, the other AZ can continue operation, ensuring uninterrupted access to critical workloads. Availability and Protection with vSANEach AZ is divided into a preferred and secondary vSAN fault domain. Under normal conditions, Virtual Machines (VMs) will use storage policies configured for dual site mirroring as well as local failures, residing in the preferred fault domain.
In case of a domain failure, vSAN powers off these VMs, and vSphere HA then powers on these VMs in the secondary fault domain. This flexibility allows administrators to apply a variety of different storage policies based on their specific requirements. |
RecognitionCategories
All
Archives
June 2024
|








 RSS Feed
RSS Feed